Documentation Index
Fetch the complete documentation index at: https://docs.runlayer.com/llms.txt
Use this file to discover all available pages before exploring further.
Managing Access Policies
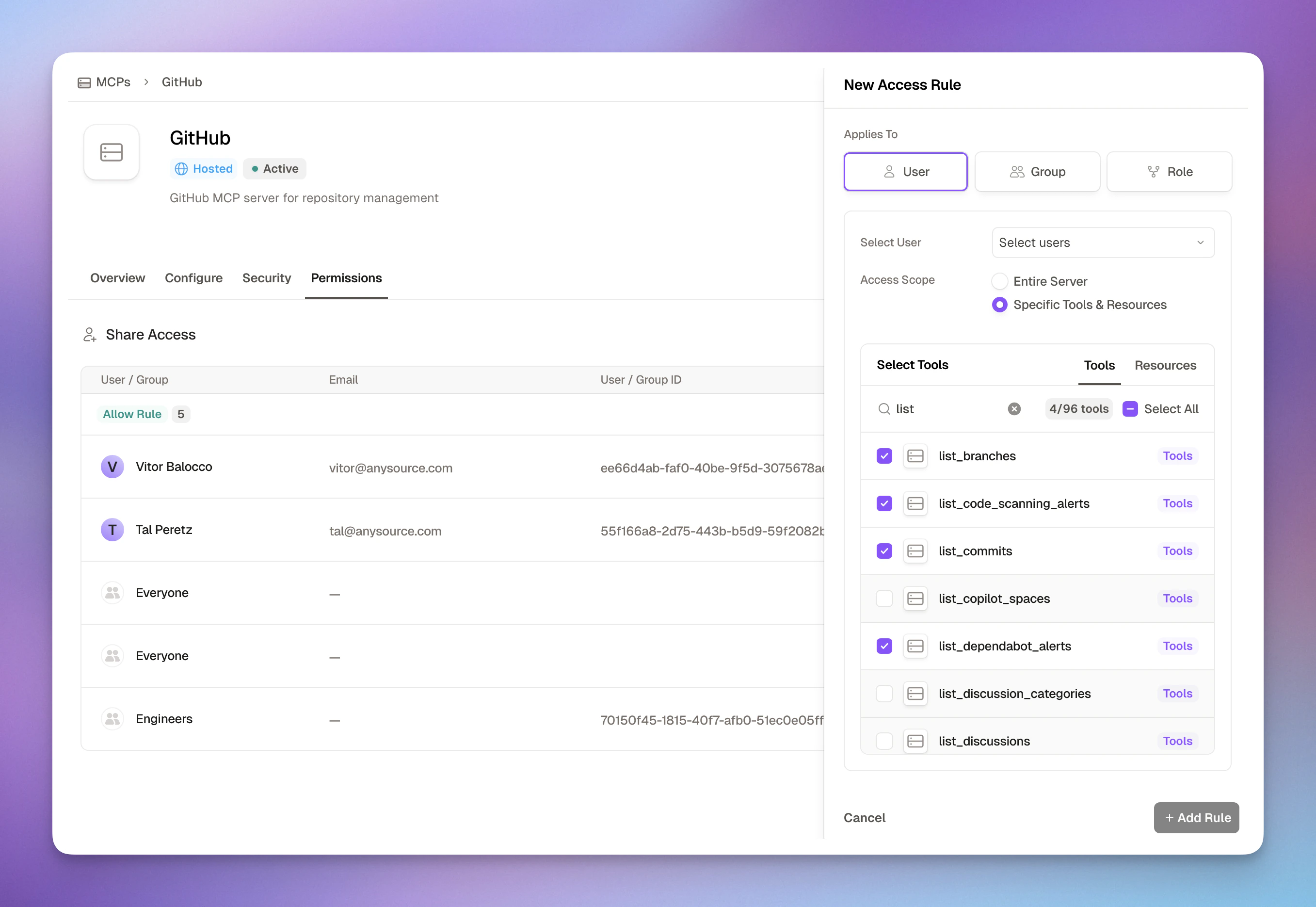
How Access Rules Work
Access rules grant permissions to users, groups, roles, or agent accounts for specific MCP servers. Each rule can include multiple principals of the same type — for example, several users or several groups in one rule. Applies To (Who gets access):- User: One or more individual employees by email/ID
- Group: One or more teams synced from your SSO (Engineering, Marketing, etc.)
- Role: One or more job functions or custom roles
- Agent Account: One or more machine-to-machine identities (see Agent Accounts)
- Attributes: Match users by identity attributes (e.g., department, job title)
- Everyone: Wildcard principal that matches all subjects, including users and agent accounts (typically used in global deny policies)
- Entire Server: Full access to all tools in the MCP
- Specific Tools & Resources: Fine-grained selection of individual tools
- Add runtime rules based on tool arguments (e.g., restrict SQL queries to specific tables)
- Enforce network restrictions (e.g., corporate IP ranges only)
- Validate OAuth session properties (e.g., require verified accounts)
- Block specific MCP clients
Policy Types
Runlayer supports two types of policies:Server-Level Policies
Manage access to specific MCP servers. Navigate to Build → [Server Name] → Policies tab.- Scope: One or more specific servers
- Action: Allow or Deny
- Use for: Granting access, fine-grained tool restrictions
- Example: Allow Finance group to use database query tools
Global Policies
Organization-wide restrictions that apply everywhere. Navigate to Admin → Policies.- Scope: All servers, tools, and resources (*)
- Action: Deny only
- Use for: IP blocks, client restrictions, compliance requirements
- Example: Block all access from outside corporate network
Creating Access Rules
Select Who Gets Access
Choose a principal type (User, Group, Role, Agent Account, or Attributes), then select one or more from the dropdown. A single rule can include multiple principals of the same type.
Define Access Scope
Choose between:
- Entire Server: Grant access to all tools (faster, simpler)
- Specific Tools & Resources: Select individual tools (more secure, granular)
Access Rule Examples
Team-Wide Server Access
Scenario: Give engineering and devops teams access to the GitHub MCP- Multiple teams need comprehensive access
- Server tools are all appropriate for the groups
- Simplicity is preferred over granularity
Fine-Grained Tool Access
Scenario: Give finance analysts read-only access to the Database MCP- Sensitive MCPs require least privilege
- Only specific tools are needed
- Different roles need different capabilities
Annotation-Based Access (Read-Only Tools)
Scenario: Give data analysts access to all tools, but only allow read-only ones at invocation time- Restrict access based on tool capabilities (read-only, destructive, etc.)
- Enforce safety boundaries at invocation time
- Works across any server with annotated tools
Individual User Access
Scenario: Give a contractor temporary access to specific Slack tools- Individual exceptions needed
- Temporary access for specific users
- Contractors or external collaborators
- Testing new MCPs with a single user first
Conditional Access by Tool Arguments
Scenario: Allow finance team to query only sales and finance tables- Database access needs table-level restrictions
- File systems need path-based access control
- APIs need parameter validation
- Sensitive data requires fine-grained control
Global Policy: Block External IPs
Scenario: Require all users to access MCPs from corporate network- Compliance requires network-based access control
- Remote work must use VPN
- Sensitive data needs IP restrictions
- Organization-wide security policy
Restrict Gmail to Internal Recipients Only
Scenario: Prevent outgoing Gmail messages to external recipients, allowing only emails sent to your internal domain (e.g.,@runlayer.com)
- Prevent data exfiltration via email in AI agent workflows
- Enforce internal-only communication for sandbox or development environments
- Provide guardrails for agents with Gmail access
- Meet compliance requirements for regulated data
- Test new AI workflows safely before allowing external communication
Block Tools That Accept Sensitive Parameters
Scenario: Prevent any tool that requires apassword parameter from being invoked
- Prevent credential-handling tools from running without approval
- Block tools with dangerous parameter shapes (e.g.,
sql,command) - Works with any
meta.tool.input_schema.*subfield (e.g.,type,required)
input_schema is the tool’s JSON Schema object. Use dot-path subfields
like meta.tool.input_schema.required with the list_contains operator,
or meta.tool.input_schema.type with equals.Block Destructive Tools Organization-Wide
Scenario: Prevent all users from invoking tools that may delete or overwrite data- Enforce safety boundaries across the organization
- Protect production data from accidental deletion
- Compliance requirements for data preservation
- Gradual rollout (start with deny-all, grant exceptions)
Dynamic Value References ($meta.* / $payload.*)
Condition values can reference runtime context dynamically by prefixing with $. This enables policies that compare one context field against another — for example, comparing a tool argument against values recorded earlier in the session.
Supported prefixes:
$payload.<field>— Resolves to the current tool call’s argument value$meta.<path>— Resolves to anymeta.*context field
- If the referenced path doesn’t exist (e.g., the tool argument isn’t present), the rule fails (does not match) — even for negated operators like
not_equalsorlist_not_contains. This prevents accidental allows when data is missing.
repo argument has not been used earlier in the session.
Session Payload Tracking
Runlayer can track which distinct tool argument values an agent uses during a session. Combined with deny policies and dynamic value references, this enables session isolation — once an agent accesses a resource (e.g., a specific repository), it cannot access different ones for the rest of the session. How it works:- A deny policy references
$payload.<field>in its value — this tells Runlayer to track that field - On each allowed tool call, the actual argument value is recorded in the session (Redis-backed, set-based)
- On subsequent calls,
meta.session.payload_values_used.<field>contains all previously-used distinct values - The deny policy evaluates against that list to block divergent values
Only fields referenced by active policies are tracked — there is no overhead for unreferenced arguments. Tracking is set-based (distinct values only, no counts or ordering).
Repository Isolation (Need-to-Know)
Scenario: Once an agent accesses a repository, block all other repositories for the rest of the session. Prevents context leakage across repos in shared agent sessions.| Rule | Purpose |
|---|---|
list_not_contains $payload.repo | Current repo is not in the set of previously-used repos |
list_regex ".+" | At least one repo has been used before (prevents blocking the very first call) |
Available Operators
Conditions use operators in snake_case. All operators are listed below:| Category | Operator | Description |
|---|---|---|
| Equality | equals | Exact match |
not_equals | Does not match | |
| String | contains | Value contains substring |
not_contains | Value does not contain substring | |
begins_with | Value starts with prefix | |
not_begins_with | Value does not start with prefix | |
ends_with | Value ends with suffix | |
not_ends_with | Value does not end with suffix | |
| Regex | regex | Matches a regular expression |
not_regex | Does not match a regular expression | |
| IP Range | ip_range | IP is within CIDR range(s) |
not_ip_range | IP is outside CIDR range(s) | |
| List | list_equals | Deep equality between lists (order-sensitive) |
list_not_equals | Lists are not deeply equal | |
list_contains | List contains value; if rule value is a list, all values must be present (subset check) | |
list_not_contains | List does not contain value; if rule value is a list, none of its values can be present | |
list_regex | List field entry matches regex | |
list_not_regex | No list entry matches regex | |
list_ip_range | List IP entry is within CIDR range(s) | |
list_not_ip_range | No list IP entry is within CIDR range(s) |
Negated operators (
not_* and list_not_*) evaluate to true when the field is missing or unavailable, following the principle that an absent value cannot satisfy the positive condition.Condition Value Matching
When writing conditions, keep these matching rules in mind:| Behavior | Details |
|---|---|
| String comparisons are case-sensitive | equals, contains, begins_with, ends_with, and regex all match exact casing. "Cursor" does not match "cursor". |
| Boolean values are case-insensitive | Fields like meta.tool.annotations.readOnlyHint or meta.subject.is_active accept true, True, or TRUE interchangeably. |
| Tool and resource names are case-sensitive | Scope entries (tools, resources) must match the exact name from the MCP server. |
| IP ranges use CIDR notation | ip_range / not_ip_range operators accept single or comma-separated CIDRs (e.g., 10.0.0.0/8, 172.16.0.0/12). |
Best Practices
Start with Specific Tools, Not Entire Server
Start with Specific Tools, Not Entire Server
When in doubt, grant access to specific tools first. You can always expand later if needed.Why?
- Easier to add permissions than remove them
- Users won’t miss tools they didn’t know existed
- Reduces attack surface if credentials are compromised
Use Groups, Not Individual Users
Use Groups, Not Individual Users
Create access rules for groups whenever possible, even if the group only has one member initially.Why?
- Scales better as teams grow
- Easier to audit (who’s in “Engineering” vs 50 individual rules)
- Syncs automatically with SSO changes
- Simplifies onboarding/offboarding
Leverage SCIM for Automatic Group Sync
Leverage SCIM for Automatic Group Sync
Runlayer automatically syncs groups from your identity provider (IDP) via SCIM, mirroring your org structure.What this means:
- Groups from Okta, Azure AD, or Google Workspace sync automatically
- New employees added to groups get access immediately
- Employees removed from groups lose access instantly
- No manual group management needed
- Create access rules using your existing IDP groups
- Engineering, Sales, Finance groups work out of the box
- Changes in your IDP reflect in Runlayer instantly
Regularly Audit Access
Regularly Audit Access
Review access rules quarterly:
- Who has access to sensitive MCPs?
- Are there users who no longer need access?
- Can we tighten tool permissions?
- Prevents scope creep
- Maintains least privilege
- Required for compliance
Use Conditions for Fine-Grained Control
Use Conditions for Fine-Grained Control
Add conditions when scope alone isn’t enough:Good use cases:
- Restrict database queries to specific tables
- Limit file access to certain paths
- Validate API parameters
- Enforce network restrictions
payload.*- Tool arguments (e.g.,payload.table,payload.path)meta.request.ip- Client IP addressmeta.request.user_agent- HTTP User-Agent header for client identificationmeta.request.method- HTTP request methodmeta.request.path- HTTP request pathmeta.subject.type- Subject type (useroragent)meta.subject.id- Subject IDmeta.subject.email- Subject email addressmeta.subject.name- Subject display namemeta.subject.roles- Assigned rolesmeta.subject.groups- Group membershipsmeta.subject.organization_id- Organization IDmeta.subject.attributes- Identity attributes (department, job title, etc.)meta.subject.is_active- Whether the subject is activemeta.user.*- Alias formeta.subject.*(backward compatibility)meta.oauth.provider- OAuth identity providermeta.oauth.scopes- OAuth scopes grantedmeta.oauth.token_expires_at- OAuth token expiry timestampmeta.server.id- Server IDmeta.server.name- Server namemeta.server.deployment_mode- Server deployment modemeta.server.auth_type- Server authentication typemeta.server.url- Server URLmeta.tool.id- Tool IDmeta.tool.name- Tool name being invokedmeta.tool.description- Tool descriptionmeta.tool.annotations.readOnlyHint- Whether the tool is read-onlymeta.tool.annotations.destructiveHint- Whether the tool is destructivemeta.tool.annotations.idempotentHint- Whether the tool is idempotentmeta.tool.annotations.openWorldHint- Whether the tool interacts with external entitiesmeta.tool.input_schema- Tool input JSON schemameta.session.servers_used- Server IDs accessed earlier in this session (list)meta.session.tools_used- Tools called earlier in this session (list, format:server_id:tool:tool_name)meta.session.scopes_used- Read/write scopes accessed earlier (list, format:server_id:scope:read|write)meta.session.payload_values_used.<key>- Distinct tool argument values used earlier in session (list, per argument name)meta.session.external_session_id- External session identifiermeta.resource.uri- Resource URImeta.resource.name- Resource name
Use Global Policies for Organization-Wide Rules
Use Global Policies for Organization-Wide Rules
Apply security controls across all resources:Common use cases:
- Block access from outside corporate network
- Restrict access to approved clients only (e.g., allow only Cursor)
- Require OAuth verification
- Enforce compliance requirements
- Global policies can only DENY (not allow)
- They apply to all servers, tools, and resources
- Manage them in Admin → Policies
- Test with small groups before applying to everyone
Related Resources
Admin Handbook
Complete policy management guide
Security
Monitor security alerts
Approvals
Review MCP requests
Security Best Practices
Security guidelines