Documentation Index
Fetch the complete documentation index at: https://docs.runlayer.com/llms.txt
Use this file to discover all available pages before exploring further.
Viewing Audit Logs
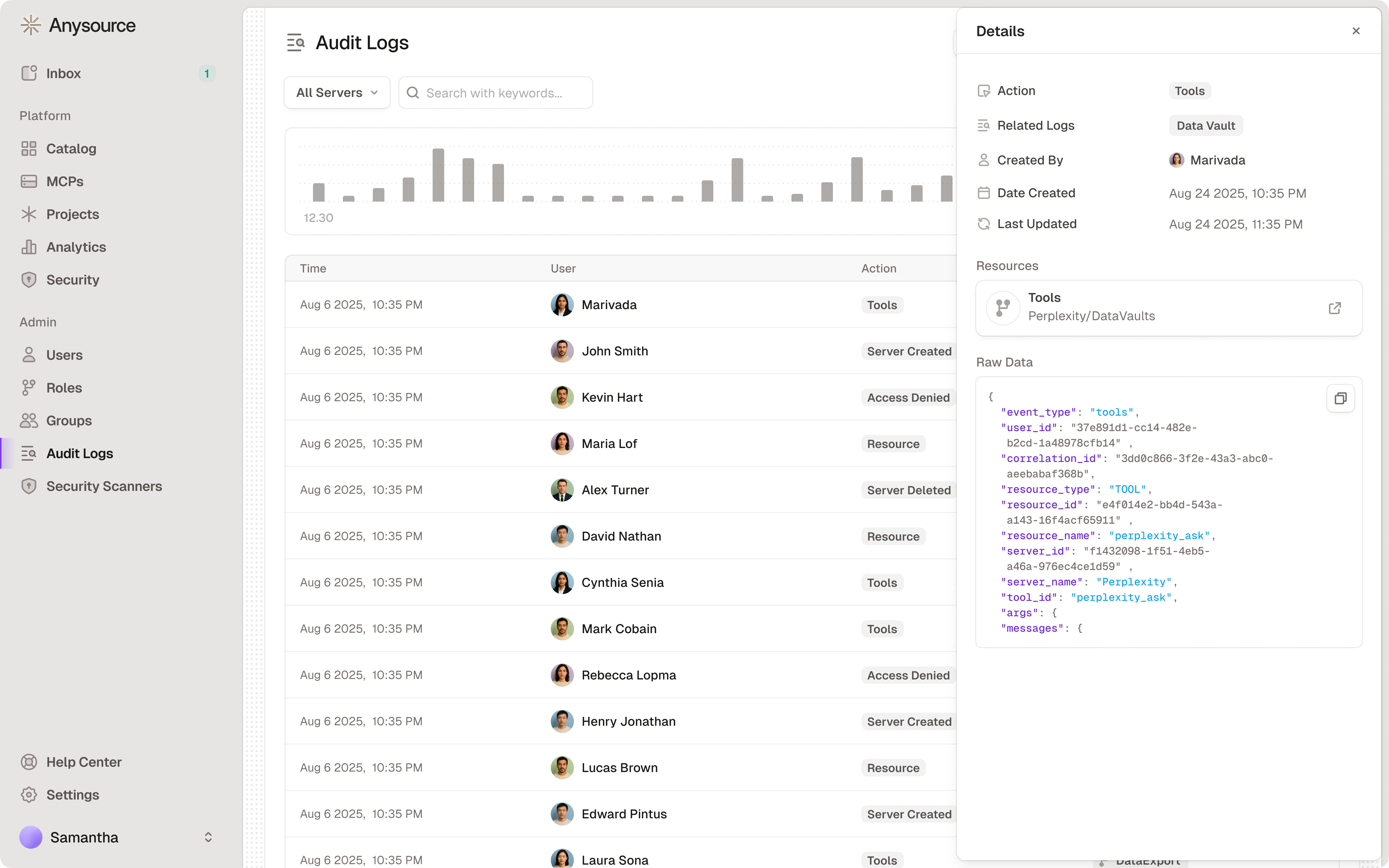
- Navigate to Audit Logs in the sidebar
- Filter by:
- Date range
- Action type (created, deleted, accessed, etc.)
- User
- Resource (specific MCP server)
- Client (MCP client application, e.g. Cursor, Claude Desktop)
- Click on any log entry to see full details
What Gets Logged
- MCP server creation, configuration, and deletion
- Skill creation, update, and deletion
- Plugin creation, update, and deletion
- Access requests and approvals
- Policy changes
- User authentication events
- Tool calls and API requests (including skill and plugin proxy calls) — tool call events include ToolGuard scan metadata (scanner name, score, duration) when security scanners are active
- Agent run lifecycle (start, success, failure) — including source, model, and duration
- Agent account lifecycle (creation, credential rotation, deletion)
- OAuth token refresh events (upstream success/failure, client-side failures)
- Security violations and risk assessments
All logs are tamper-proof and retained for compliance purposes.
Sensitive Connector Redaction
Connectors that handle highly sensitive data (e.g. HR systems, financial databases) can be marked as sensitive by a Super Admin. When enabled, tool call arguments, results, errors, and security scan details are automatically redacted from audit log entries for that connector.What gets redacted
| Event type | Redacted fields |
|---|---|
| Tool calls and resource access | args, result, error |
| Security violations and warnings | scan_input, area_of_concern, detected_items |
Enabling sensitive mode
- Navigate to the connector’s settings (Super Admin only)
- Enable Sensitive audit log
- Optionally select viewer roles that should see unredacted data
- Save — redaction takes effect immediately for all future and existing log entries
Redaction is applied at read time, not at write time. The underlying audit log data is unchanged. If you later disable sensitive mode or add a viewer role, previously redacted entries become visible again.
Querying from the CLI
Theuvx runlayer logs command lets you query audit logs from the terminal. By default it shows your own events from the last 7 days.
Options
| Flag | Description |
|---|---|
--type, -t | Filter by action type(s). Comma-separated or use shortcuts: auth, tools, security, servers, agents |
--server-id | Filter by MCP server UUID |
--agent-id | Filter by agent account UUID |
--client-name | Filter by client name in event details |
--user-id | Filter by user ID (admin only, defaults to self) |
--all | Show all users’ logs (admin only) |
--start | Start time (ISO 8601). Default: 7 days ago |
--end | End time (ISO 8601). Default: now |
--limit, -n | Max events to return (default 50, max 2000) |
--json | Output raw JSON for scripting |
Examples
--limit, the CLI prints a next-page command you can copy-paste to continue paginating.
SIEM Export (S3)
Runlayer can continuously export audit logs to an S3 bucket for ingestion into your SIEM (e.g. CrowdStrike NG-SIEM, Splunk, Sentinel). Once enabled, every audit event is written as a gzip-compressed JSON file to the configured bucket in near real-time.How it works
- Runlayer pushes to S3 — each audit log is enqueued to an internal outbox and asynchronously exported as a
.json.gzfile. There is no polling or pull mechanism required on Runlayer’s side; logs land in the bucket automatically. - You provide a cross-account IAM role — your team creates an IAM role in your AWS account and supplies the Role ARN to Runlayer. Runlayer’s export worker assumes that role to write objects into your bucket.
- Your SIEM reads from the bucket — point your SIEM’s S3 connector (e.g. CrowdStrike’s S3 data connector) at the bucket. Most SIEMs support S3 as a native log source.
S3 object layout
Objects are written with a Hive-style date partition prefix:Payload schema
Each exported file contains a single JSON object:Getting started
To enable SIEM export for your organization, contact your Runlayer account team. You will need to:- Create an S3 bucket in your AWS account for audit log delivery.
- Create an IAM role that trusts Runlayer’s AWS account and grants
s3:PutObjecton the bucket. - Share the Role ARN and bucket name with Runlayer so the feature can be enabled for your environment.
The S3 export is independent of the in-app audit log viewer and the CSV/JSON download export. All three can be used simultaneously.
Related Resources
Security
Monitor security alerts
Employee Handbook
Complete user guide