Documentation Index
Fetch the complete documentation index at: https://docs.runlayer.com/llms.txt
Use this file to discover all available pages before exploring further.
Security Monitoring
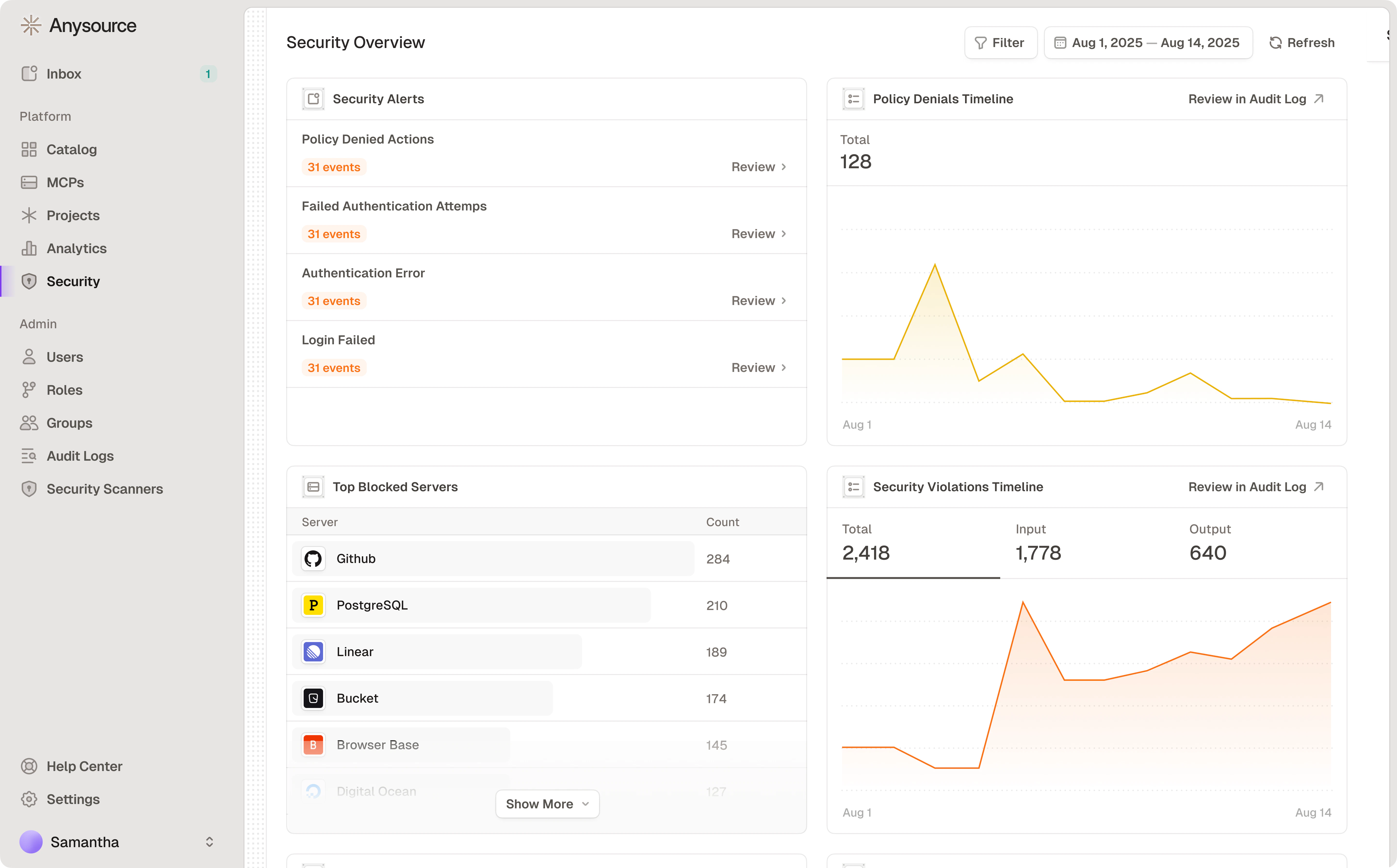
Dashboard Components
Security Alerts - Click “Review” to see details in Audit Logs:- Policy Denied Actions
- Failed Authentication Attempts
- Authentication Error
- Login Failed
- High counts may indicate missing access policies
- May need access or training
- Input: Suspicious requests to MCPs
- Output: Suspicious responses from MCPs
- Includes activity from both users and Agents
Hidden-character masking and sensitive-token masking events are classified as security warnings rather than violations. They still appear in audit logs and analytics but are separated from higher-severity violations in the dashboard.
Responding to Issues
High blocks for one user: Grant access or investigate unauthorized attempts High blocks for one server: Review if team needs access Spike in violations: Potential security incident - escalate Repeated auth failures: Fix credentials or detect attackRelated Resources
Audit Logs
View detailed activity logs
Security Best Practices
Security guidelines